Expressvpn Glossary
Remote access trojan
What is a remote access trojan?
A remote access trojan (RAT) is malware that secretly establishes remote control of an infected device, enabling an attacker to access and operate the system without authorization. Its core purpose is to provide covert remote access for activities such as data theft, surveillance, or further compromise.
How does a remote access trojan work?
After installation, a RAT runs a hidden client component in the background. It connects to attacker-controlled command-and-control (C2) servers to establish a remote control channel. Through this channel, the RAT receives commands to execute on the device and sends stolen data back to the attacker.
Many RATs also establish persistence through startup items, scheduled tasks, registry run keys, or system services, so they continue running after reboots or logons.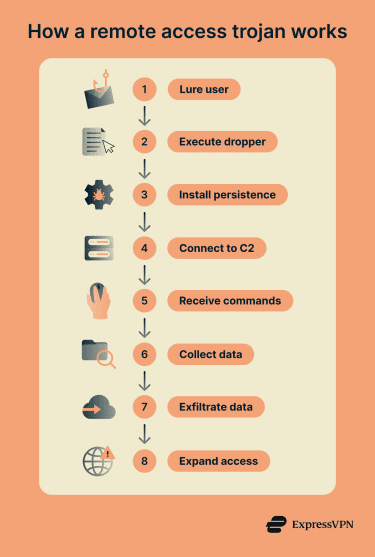
How are remote access trojans commonly delivered?
- Phishing campaigns: Malicious links or attachments delivered through email (and sometimes text or social platforms) are used to install RATs.
- Fake downloads and trojanized installers: RATs may be embedded in legitimate-looking downloads, including bundled installers and compromised software packages.
- Malvertising and drive-by download sites: Malicious ads and compromised or deceptive sites can deliver RAT payloads through redirects and or download prompts.
- Pirated software and crack bundles: RATs are commonly distributed via illegal software downloads, keygens, and cracks that are packaged with malware.
- Attacks on remote workers and small organizations: RATs are used to compromise endpoints and then expand deeper into organizational networks.
Types of remote access trojans
- RATs offered through Malware-as-a-service (MaaS): Some RAT operators sell or rent access through criminal marketplaces, often packaging the malware with infrastructure and support for buyers.
- Custom RATs used in advanced persistent threat (APT) operations: Well-resourced groups may use custom RATs to maintain long-term access, commonly for espionage or strategic objectives.
- Mobile RATs: RATs designed for smartphones and tablets, often focused on monitoring device activity, stealing credentials, and, in some cases, accessing messages or notifications depending on platform permissions and privileges.
- Modular RATs: RATs built around a core component that can load plug-ins to add capabilities as needed.
- Abused remote access tools: Legitimate remote administration or support software can be misused to provide unauthorized access and control, though the software itself is not inherently a trojan.
Why is a remote access trojan dangerous?
A RAT is dangerous because it provides attackers with sustained, interactive control over a compromised device, making it a reliable platform for broader attacks. It can enable account compromise by stealing credentials, cookies, and authentication tokens, which in some cases may let attackers continue accessing accounts without re-entering a password until those sessions or tokens expire or are revoked.
It can also support surveillance, data theft, ransomware deployment, and other follow-on activity. The impact can extend beyond a single device, affecting both individuals and businesses through financial loss, operational disruption, and expanded breach scope.
Risks and privacy concerns
RATs can create direct privacy exposure by enabling covert monitoring of webcams, microphones, and screens, depending on the malware’s capabilities and the permissions or privileges it obtains. They can also capture inputs via keylogging and clipboard theft, increasing the risk of account compromise, financial fraud, and identity theft.
They may also support bulk data collection and exfiltration, creating leverage for extortion when sensitive files, messages, or business records are taken. In organizational settings, a RAT can also serve as a foothold for lateral movement within a network, increasing the likelihood that additional devices, accounts, and internal systems are compromised.
Further reading
- What is Trojan malware? Full guide to risks and protection
- How to know if your computer has a virus (Windows and Mac)
- What is spyware? Types, examples, and how to prevent it
- What is a keylogger, and how does it work?
- What is a rootkit, and why is it so dangerous?

